Reconnaissance Project
2023 | User Research, Workshop facilitation, Interaction design
Overview
Many organizations do not have full control of their attack surface. Application security management (ASM) tools help by identifying and continuously tracking all digital assets, so this is not done manually.
However, security teams often lack the needed visibility and contextual awareness to protect mission-critical digital assets. They can be overwhelmed with information yet struggle to identify and defend their attack surface.
This is where Hacker Reconnaissance comes in - to help organizations understand and prioritize the most important aspects of their attack surface by leveraging the expertise of hackers.
Project context
Hacker Reconnaissance started as an experiment and, after a number of interactions, it was decided to invest more in it. In the last months at Hackerone, I got involved in this project. My role was to find ways to make it scalable and incorporate the entire workflow into the platform so that hackers and customers could take part in it.
If you'd prefer to skip the process and go straight to the final results, click the button below
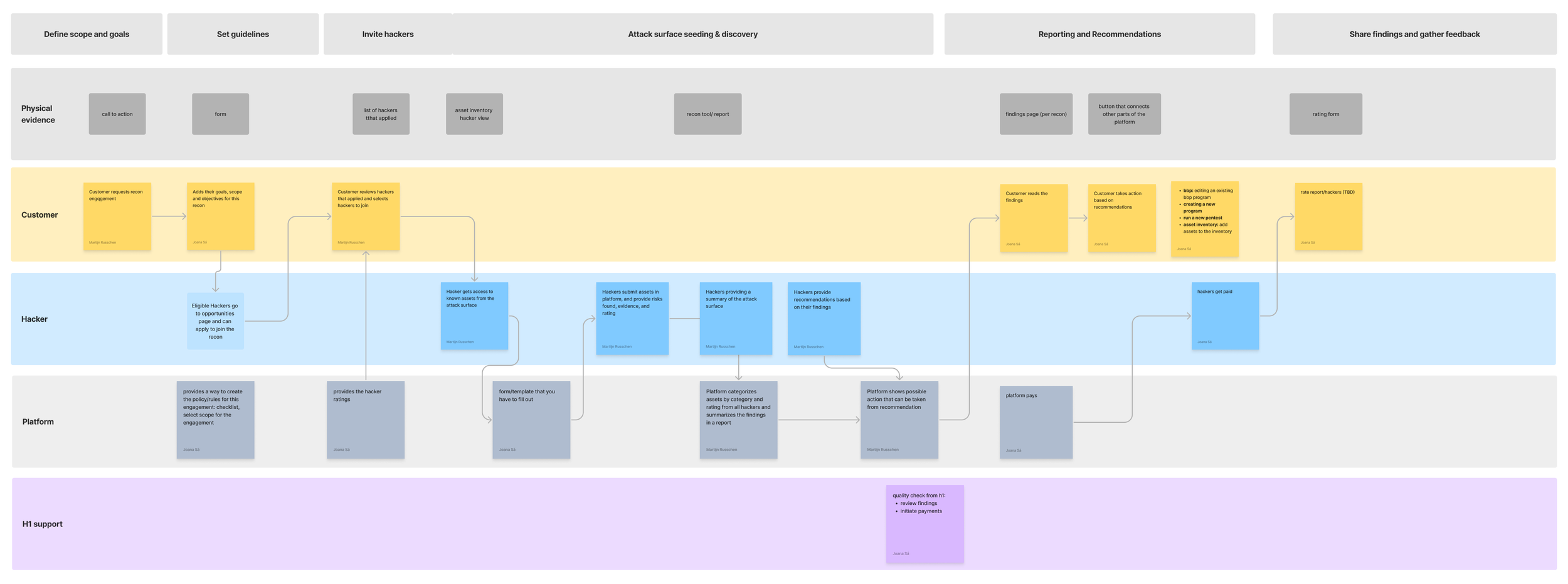
Mapping the process
With the assistance of key stakeholders, I started the process of mapping out the entire workflow. This included outlining every activity undertaken at each stage by the various roles involved, as well as examining their interactions. The existing workflow was characterized by extensive manual labor and significant resource allocation.
After that, I pinpointed the most challenging areas within the flow. These issues encompassed a range of concerns, including tasks consuming excessive time, processes lacking scalability, and elements that did not meet security compliance standards.
The ideal flow
To achieve a shared vision for the project, I brought together the product manager and technical lead to collaborate on shaping the ideal flow. Our objective was to tackle any issues in the process by brainstorming creative ideas. During this session, we deliberately avoided constraining our thinking and explored wild concepts without immediate concern for technical feasibility. This approach was meant to be followed by more detailed evaluation in subsequent project phases.
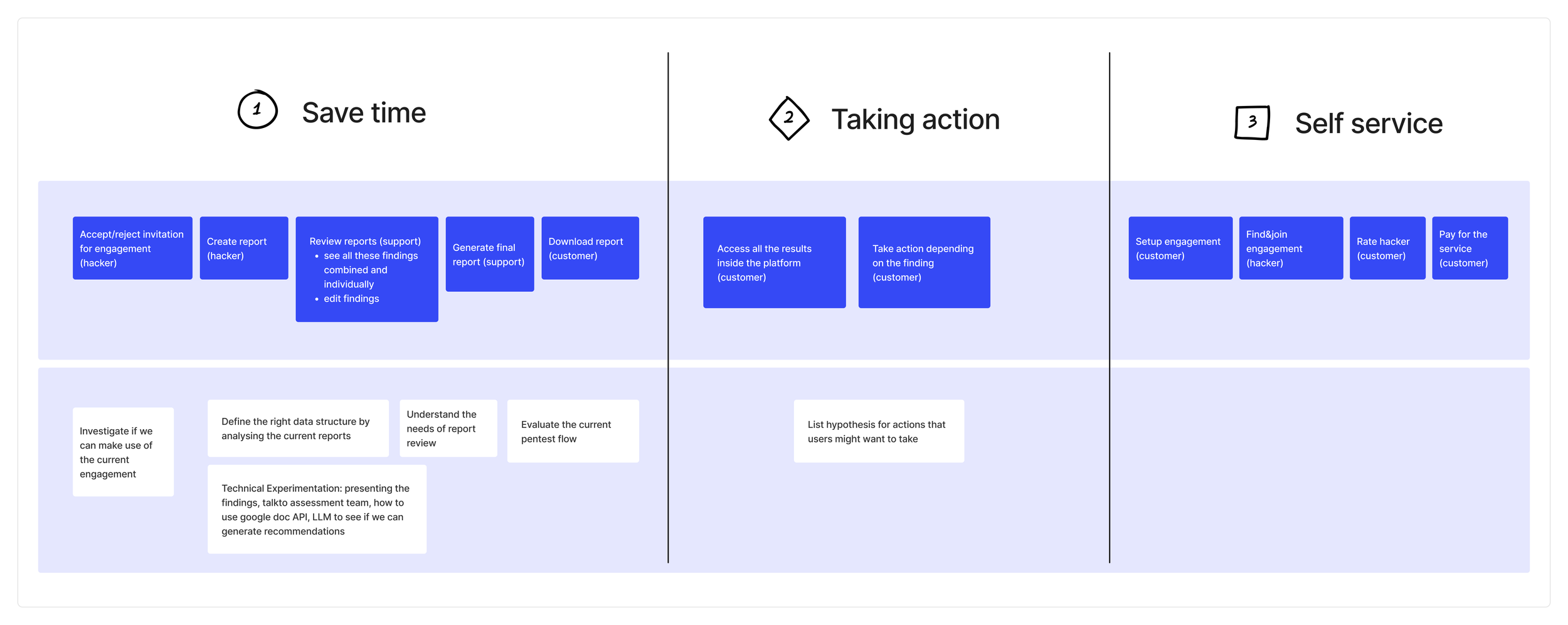
Breakdown in phases
After getting the entire team on board with a clear sense of direction, the next step was to break down the work into phases. We defined three main themes:
Time-saving: This includes opportunities that would immediately reduce the amount of time and resources spent during reporting.
Taking action: This involves opportunities related to how to better consume the findings.
Self-service process: This includes automating any remaining manual workflows so we wouldn’t have to allocate any additional resources.
Save time - zooming in
Previously, all communication between HackerOne and hackers was done through email. We evolved this process by assigning someone to be in constant communication with each hacker, checking and replying to emails, and supporting them throughout the flow. Additionally, the report itself didn't have to follow any particular structure. Since the final report sent to customers was a combination of several hacker reports, someone had to invest a lot of time analyzing each report individually and merging them into a single report.
There were several opportunities to optimize this process, such as streamlining the hacker report workflow, which would also help us optimize the review workflow.
From the hacker's side, the entire reporting workflow should be incorporated into the platform. This should include getting invited, joining the program, creating and submitting reports, and receiving payment. Hackers should also be required to follow a specific structure when documenting their findings.
From the reviewer's side, once the reports are completed, they can access and combine them into a single report. AI capabilities can be used to speed up this process, allowing the reviewer to only review the final result and submit the report for customers to access.
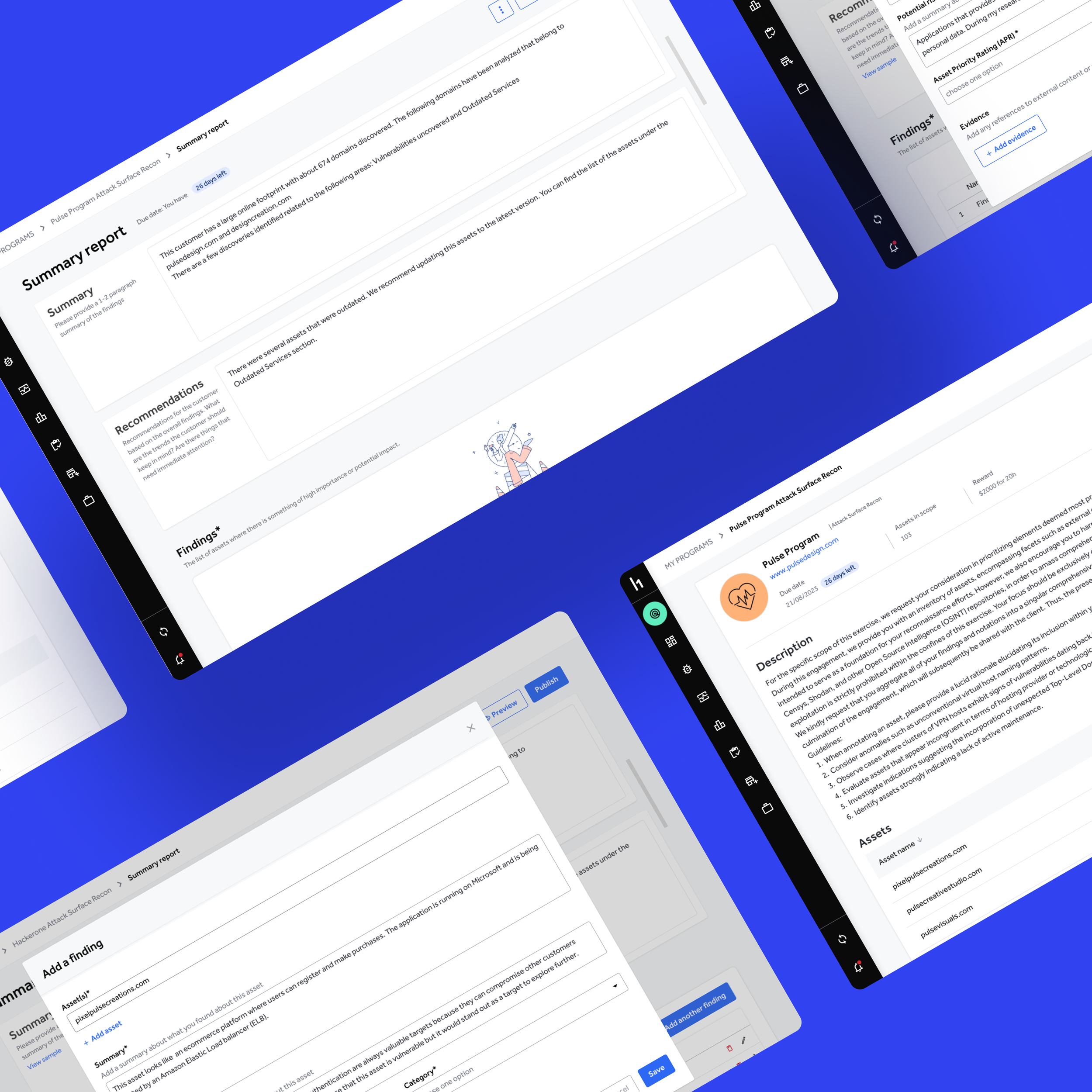
Designs
To illustrate the task flow of the hacker while creating a report I created this prototype that takes us through the different steps. The idea was to test the prototype with hackers and based on the feedback iterate on it. We wanted to validate if our solution would help with their workflow of submitting reports. Unfortunately, I didn’t have the opportunity to continue this project so this was my last contribution.
Closing offs
Having a shared vision while allowing room for creativity sets a clear path for everyone in the team. Mapping the ideal flow served as a guide throughout the project and helped us to run in the same direction while still being flexible because things can change along the way.
You can achieve great things with collaboration. Even though I didn’t have a chance to continue this project I think what we did up to this point was a good example of how you can get good results when you merge diverse perspectives and combine different strengths together.